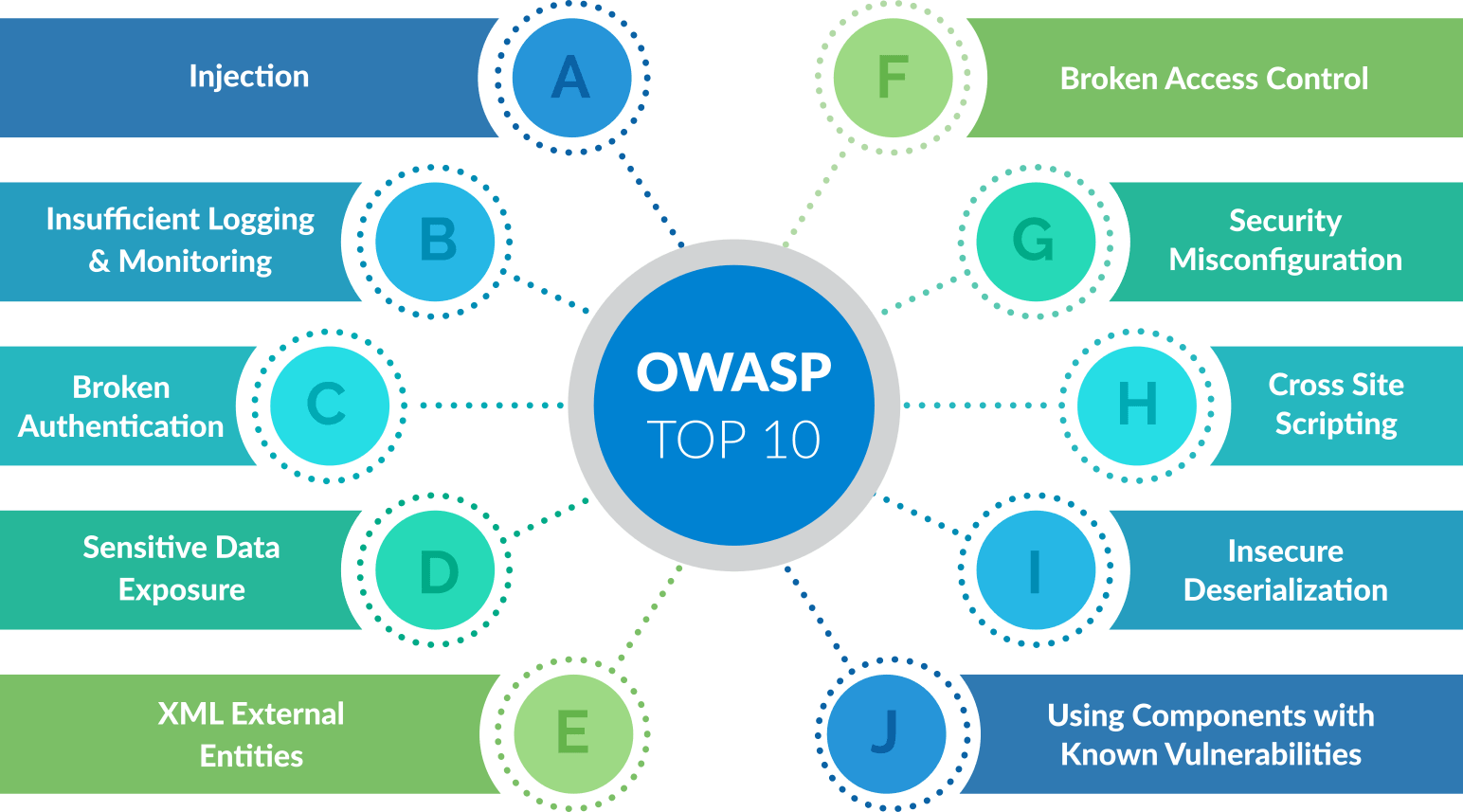
I. Introduction to OWASP Top 10
Overview of OWASP (Open Web Application Security Project)
OWASP (Open Web Application Security Project) is a non-profit organization that focuses on improving the security of web applications. It provides resources, tools, and guidelines to help developers and organizations build and maintain secure web applications.
Purpose and importance of OWASP Top 10 in infosec cybersecurity
The OWASP Top 10 is a list of the top ten most critical web application security risks. It serves as a guide for developers, security professionals, and organizations to understand and address common vulnerabilities in web applications. The list is updated periodically to reflect the evolving threat landscape.
The OWASP Top 10 is important for infosec cybersecurity because:
- Awareness: It raises awareness about the most prevalent web application vulnerabilities and helps developers understand the potential risks they may face.
- Prevention and mitigation: By following the guidelines provided in the OWASP Top 10, organizations can implement necessary measures to prevent and mitigate web application security risks.
- Compliance: Many industry regulations and standards, such as PCI DSS, require organizations to address the vulnerabilities listed in the OWASP Top 10. Compliance with these standards helps ensure the security of sensitive data.
- Educational resource: The OWASP Top 10 provides valuable educational resources, including documentation, training materials, and best practices, to help developers and security professionals improve their understanding of web application security.
By including the OWASP Top 10 as part of their cybersecurity practices, organizations can significantly enhance the security of their web applications and protect sensitive data from potential threats.
II. Injection Attacks
Explanation of injection attacks
Injection attacks are a common type of security vulnerability that can compromise the integrity and security of a system. They occur when an attacker is able to inject malicious code or commands into a vulnerable application, allowing them to manipulate or access sensitive data. Injection attacks can target various areas of an application, including databases, command shells, and XML parsers. The impact of such attacks can range from unauthorized data disclosure to complete system compromise. It is crucial for organizations to understand and address injection vulnerabilities to protect their systems and data.
Examples of injection attacks
Some common examples of injection attacks include:
- SQL Injection: In this type of attack, attackers manipulate SQL queries to access or modify data in a database.
- Command Injection: Attackers inject malicious commands into a vulnerable application, allowing them to execute arbitrary commands on the underlying operating system.
- Cross-Site Scripting (XSS): Attackers inject malicious scripts into web pages, which are then executed by users’ browsers.
- XML Injection: Attackers manipulate XML inputs in web applications to access or modify sensitive information.
Mitigation techniques for injection attacks
To mitigate the risk of injection attacks, organizations can implement several security measures:
- Input validation: Validate and sanitize all inputs to prevent attackers from injecting malicious code.
- Parameterized queries: Use prepared statements or parameterized queries in database interactions to prevent SQL injection attacks.
- Output encoding: Encode all output to prevent cross-site scripting attacks.
- Security awareness training: Educate developers and other stakeholders about the risks and best practices for preventing injection attacks.
- Regular security testing: Perform regular vulnerability assessments and penetration tests to identify and address any injection vulnerabilities.
By implementing these mitigation techniques, organizations can significantly reduce the risk of injection attacks and safeguard their systems and data from potential exploitation
III. Broken Authentication and Session Management
Understanding broken authentication and session management vulnerabilities
Broken authentication and session management vulnerabilities are a critical aspect of web application security. These vulnerabilities occur when authentication mechanisms, such as passwords or session tokens, are not implemented correctly, leaving them vulnerable to attacks. Here are some key points to understand about these vulnerabilities:
- Authentication vulnerabilities: These vulnerabilities involve issues with user authentication, such as weak passwords, predictable password resets, or ineffective session management.
- Session management vulnerabilities: These vulnerabilities occur when sessions are not properly managed, allowing unauthorized access to user accounts or the ability to hijack sessions.
- Common causes: Incorrectly implemented login mechanisms, insufficient session expiration controls, weak password reset mechanisms, and the use of insecure storage for session data can all contribute to broken authentication and session management vulnerabilities.
Impacts of these vulnerabilities
The impacts of broken authentication and session management vulnerabilities can be severe, potentially leading to unauthorized access to user accounts, sensitive data exposure, identity theft, or account takeovers. These vulnerabilities can also lead to session hijacking, where an attacker gains control over a user’s active session, allowing them to perform actions on behalf of the user without their knowledge.
Best practices for securing authentication and session management
Securing authentication and session management is crucial for protecting user accounts and sensitive data. Here are some best practices to mitigate these vulnerabilities:
- Implement strong authentication mechanisms: This includes enforcing strong password policies, implementing multi-factor authentication, and utilizing secure password storage techniques.
- Implement secure session management: Ensure session IDs are sufficiently random and unpredictable, use HTTPS for secure communication, and implement proper session expiration and invalidation controls.
- Regularly test and patch: Regularly test for vulnerabilities, such as session fixation or session ID leaks, and promptly apply patches and updates to address any security issues.
- Monitor and detect anomalies: Implement monitoring mechanisms to detect suspicious activities, such as multiple failed login attempts or unusual session behavior.
By following these best practices, organizations can significantly reduce the risk of broken authentication and session management vulnerabilities and enhance the security of their web applications.
For more information about OWASP Top 10 and web application security, you can visit the official OWASP website here.
IV. Cross-Site Scripting (XSS)
Overview of XSS attacks
Cross-Site Scripting (XSS) is a type of security vulnerability that allows attackers to inject malicious scripts into web pages viewed by other users. This can happen when a website does not properly validate or sanitize user-generated input, thereby allowing the attacker to input harmful code that is executed by the victim’s browser. XSS attacks can have various consequences, such as stealing user data, impersonating users, or even taking control of their accounts.
Different types of XSS attacks
There are three main types of XSS attacks:
1. Stored XSS: In a stored XSS attack, the malicious script is permanently stored on a target website, such as in a comment or a forum post. When other users view the affected page, the script is executed, potentially compromising their security.
2. Reflected XSS: Reflected XSS attacks occur when the malicious script is embedded in a URL or input field, and the server reflects it back to the user without proper sanitization. When the user clicks on the manipulated link or submits the form, the script is executed in their browser.
3. DOM-based XSS: DOM-based XSS attacks exploit vulnerabilities in a website’s Document Object Model (DOM) manipulation by injecting malicious scripts that manipulate the webpage’s DOM structure. This can lead to unauthorized actions or data manipulation.
Preventive measures against XSS attacks
To protect against XSS attacks, developers and website administrators can take the following preventive measures:
1. Input validation and sanitization: Validate and sanitize all user-generated input to ensure that it does not contain any malicious code. This can involve using security libraries or implementing custom validation and sanitization routines.
2. Output encoding: Properly encode all user-generated content or output to prevent potential XSS attacks. This involves converting special characters into their HTML entities to prevent them from being interpreted as code.
3. Content Security Policy (CSP): Implementing a Content Security Policy can help mitigate XSS attacks by specifying which sources of content are considered trusted. This can restrict the execution of potentially harmful scripts.
4. Regular security updates: Keep all software, frameworks, and libraries up to date with the latest security patches. This ensures that any known vulnerabilities, including those related to XSS, are addressed.
5. Educating users: Raise awareness among users about the risks of XSS attacks and teach them safe browsing habits. Encourage users to review URLs before clicking on them and to be cautious when entering personal information on websites.
By implementing these preventive measures, organizations can significantly reduce the risk of XSS attacks and protect the integrity and security of their web applications.
For more information on XSS attacks, you can visit the OWASP website.
V. Insecure Direct Object References
Explanation of insecure direct object references
Insecure Direct Object References (IDOR) refer to vulnerabilities that occur when an application’s code allows unauthorized access to internal resources or data by directly referencing them without proper authentication or authorization checks. This means that attackers can bypass security measures and access sensitive information or perform actions that they should not have permission to perform.
The primary cause of insecure direct object references is inadequate validation of user input or insufficient access control mechanisms. By manipulating parameters in the URL or form data, attackers can modify object references and gain unauthorized access to resources.
For example, if a website has a URL like “www.example.com/user/profile?id=123,” an attacker could change the parameter to “id=456” to access another user’s profile without proper authorization.
Insecure direct object references are critical security issues that can lead to unauthorized data exposure, privilege escalation, or even complete system compromise. Proper access controls and input validation techniques are crucial in preventing these vulnerabilities and protecting sensitive data from unauthorized access.
To learn more about Insecure Direct Object References, visit the OWASP website.
 Source: www.infosectrain.com
Source: www.infosectrain.comVI. Security Misconfigurations
What are security misconfigurations?
Security misconfigurations refer to the incorrect or incomplete configuration of security settings and controls in software applications, servers, or network devices. These misconfigurations can leave systems vulnerable to cyber attacks and compromise the confidentiality, integrity, and availability of sensitive data.
Common examples of security misconfigurations include:
- Leaving default passwords or credentials unchanged, making it easier for attackers to gain unauthorized access.
- Not applying necessary security patches and updates, leaving systems exposed to known vulnerabilities.
- Improperly configuring access controls, allowing unauthorized users to access sensitive information.
- Failing to properly set up firewalls and network security settings, leaving networks open to intrusions.
It is crucial to address security misconfigurations as part of any comprehensive cybersecurity strategy to reduce the risk of data breaches and cyber attacks. Regular security audits and vulnerability assessments can help identify and fix these misconfigurations, ensuring that systems are properly configured to protect against potential threats.
Understanding CSRF attacks
Cross-Site Request Forgery (CSRF) is a type of attack that occurs when a malicious website tricks a user’s browser into making unintended requests to another website. The attacker can exploit the user’s authenticated session on the targeted website to perform unauthorized actions without the user’s knowledge or consent.
Impact of CSRF attacks
CSRF attacks can have severe consequences for both users and targeted websites. Some potential impacts include:
- Unauthorized actions: Attackers can perform actions on behalf of the user without their knowledge, such as changing passwords, making purchases, or deleting important data.
- Data theft: Attackers can trick users into revealing sensitive information by redirecting them to malicious websites that mimic legitimate ones.
- Compromised accounts: If a user is tricked into carrying out malicious actions, their account could be compromised, leading to further security breaches.
- Reputation damage: CSRF attacks can damage the reputation of targeted websites, leading to a loss of trust from users.
Prevention techniques for CSRF attacks
To protect against CSRF attacks, websites can implement various prevention techniques:
- Implementing CSRF tokens: Websites can generate and include a unique and unpredictable token in each request. This token is then verified on the server-side to ensure that the request originated from a legitimate source.
- SameSite cookies: Setting the SameSite flag on cookies can prevent the browser from sending cookies in cross-site requests, mitigating the risk of CSRF attacks.
- User awareness and education: Educating users about the risks of CSRF attacks and promoting best practices, such as not clicking on suspicious links or accessing sensitive accounts on shared devices, can help prevent successful attacks.
- Security testing: Regular vulnerability assessments and penetration testing can help identify and address any potential CSRF vulnerabilities in a proactive manner.
By implementing these prevention techniques, websites can significantly reduce the risk of CSRF attacks and enhance the overall security of their users’ data and accounts.
VIII. Using Components with Known Vulnerabilities
Explanation of risks associated with using components with known vulnerabilities
Using components with known vulnerabilities can pose significant risks to the security of an organization’s information system. Here are some key points to consider:
1. Exploitation: Attackers actively scan for vulnerable components and exploit known vulnerabilities to gain unauthorized access to systems.
2. Data Breaches: Vulnerable components can provide an entry point for attackers to steal sensitive data, including customer information, financial records, and intellectual property.
3. Malware Injection: Attackers can exploit vulnerabilities in components to inject malware or malicious code into systems, leading to system compromise or unauthorized activities.
4. Compliance Violations: Organizations that fail to address vulnerabilities in components may face compliance violations with industry regulations and legal requirements.
Methods to identify and mitigate vulnerabilities in components
To mitigate the risks associated with using components with known vulnerabilities, the following measures can be taken:
1. Regular Patching and Updates: Keep all components and software up to date with the latest patches and security updates to address known vulnerabilities.
2. Vulnerability Scanning and Assessments: Regularly scan systems and components using vulnerability assessment tools to identify and prioritize vulnerabilities for remediation.
3. Monitoring Security Advisories: Stay informed about new vulnerabilities by monitoring security advisories from vendors, industry forums, and the Open Web Application Security Project (OWASP).
4. Implement Secure Component Management: Use a centralized component management system that tracks and monitors the components used in software development, making it easier to identify and mitigate vulnerabilities.
By addressing vulnerabilities in components, organizations can significantly reduce the risk of security breaches and ensure the ongoing protection of their information systems.
Significance of OWASP Top 10 in information security and cybersecurity
The OWASP Top 10 is a crucial resource in the field of information security and cybersecurity. It provides a comprehensive list of the most critical web application security risks that organizations should be aware of and address. By understanding these vulnerabilities and implementing appropriate security measures, organizations can significantly reduce the risk of cyberattacks and safeguard their sensitive data.
Key takeaways and recommendations for implementing OWASP Top 10 best practices
Here are some key takeaways and recommendations for implementing the OWASP Top 10 best practices:
- Stay updated: Regularly check for updates and revisions to the OWASP Top 10 list to ensure that your organization is aware of the latest security risks.
- Conduct risk assessments: Perform comprehensive risk assessments to identify potential vulnerabilities in your web applications and prioritize mitigation efforts.
- Implement secure coding practices: Train developers on secure coding practices and encourage the adoption of security best practices throughout the software development lifecycle.
- Employ vulnerability scanning and penetration testing: Regularly scan your web applications for vulnerabilities and conduct penetration tests to identify potential security weaknesses.
- Implement a robust firewall and intrusion detection system: Utilize firewalls and intrusion detection systems to monitor and filter incoming and outgoing network traffic, providing an added layer of protection.
By following these recommendations and implementing the OWASP Top 10 best practices, organizations can enhance their overall cybersecurity posture and protect their web applications from potential threats.
For more information on OWASP and its initiatives, you can visit the OWASP website.